The telemechanique server provides:
- data collection protocols IEC 61850(MMS), IEC 60870-5-104, Modbus TCP/RTU;
- collection of diagnostic information from equipment via SNMP protocol;
- data transmission via IEC 60870-5-101/104 protocols to the grid control center, dispatching control room;
- group alarm function;
- management capture function;
- verification function.
The telemecanique server collects data from telemecanique devices, PAC and adjacent systems via digital communication channels using IEC 61850 (MMS), IEC 60870-5-104, SNMP, Modbus TCP/RTU protocols.
The server includes at least two Ethernet digital exchange modules (Fx/Tx) that meet the requirements of the IEEE 802.3 Ethernet standard, support RSTP or PRP redundancy technologies, and have the ability to collect and process data from devices that do not support Ethernet transmission (e.g. Modbus RTU) using an external interface converter.
The telemechanique server provides the issuance of information according to IEC 60870-5-101/104 protocols. Data transmission can be carried out in several directions with the ability to set a different number and different addressing of telesignals in each direction, with the possibility of implementing the capture of management function, taking into account access rights.
The telemecanique server has the ability to generate group signaling based on signals from various sources.
On the telemechanique server, the «Management capture» function is implemented. To block the simultaneous control of the substation equipment on the telemechanique server, a software «Remote control key» is provided, which allows at one time control of the substation equipment from only one place.
The software «Remote control key» can have five positions:
- «Released» – remote control is not carried out, it is possible to transfer the "Remote control key" to any of the provisions below;
- «Substation» – switching is carried out from the substation;
- «Joint dispatching management» – remote control of the substation is carried out from the joint dispatching management;
- «Regional dispatching control» – remote control of the substation is carried out from the regional dispatching control;
- «Grid control center» – remote control of the substation is carried out from the grid control center.
Normally, the «Remote control key» is set to the «Released» position. In the joint dispatching management, regional dispatching control, grid control center, information about the current position of the «Remote control key» is transmitted. In the event of failure of one of the telemechanique servers (in case of redundancy) or in case of failure of one of the communication channels, the «Telemechanique key» retains its state.
The function of verification or checking the reliability of analog signals is used when there are two or more sources of analog signals to calculate the resulting signal, taking into account the quality of the signal and the presence of communication with the device.
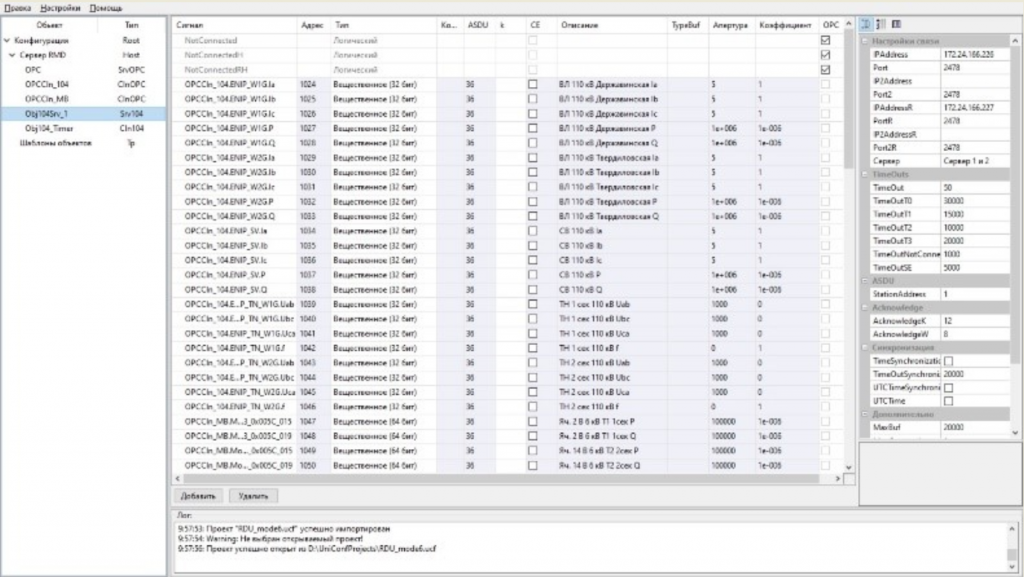
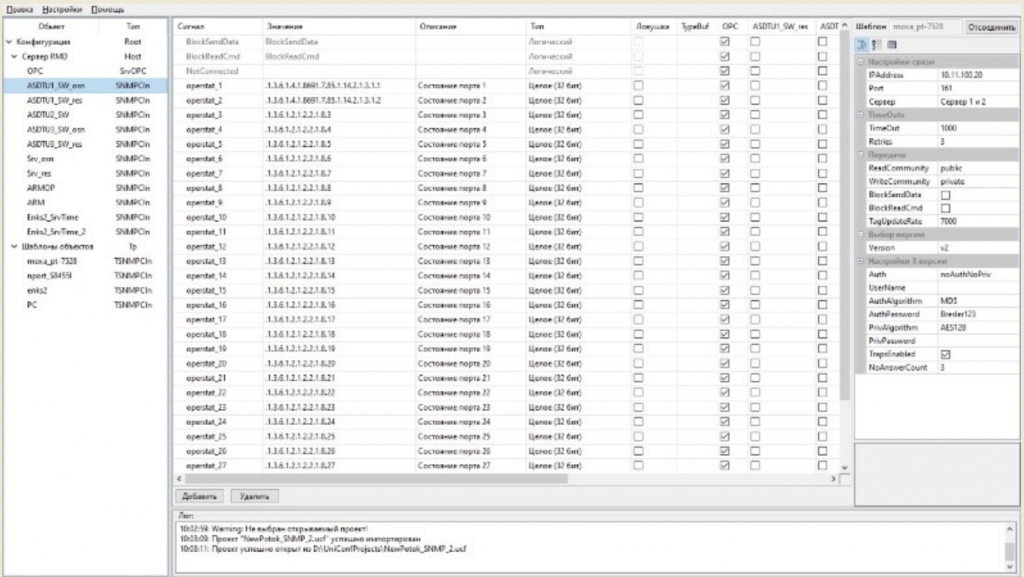
To configure the STM-RLMK, specialized «UniConf» software is used:

Window of setting for receiving data according to IEC 61850
|

Window of setting for receiving data according to ModBus
|
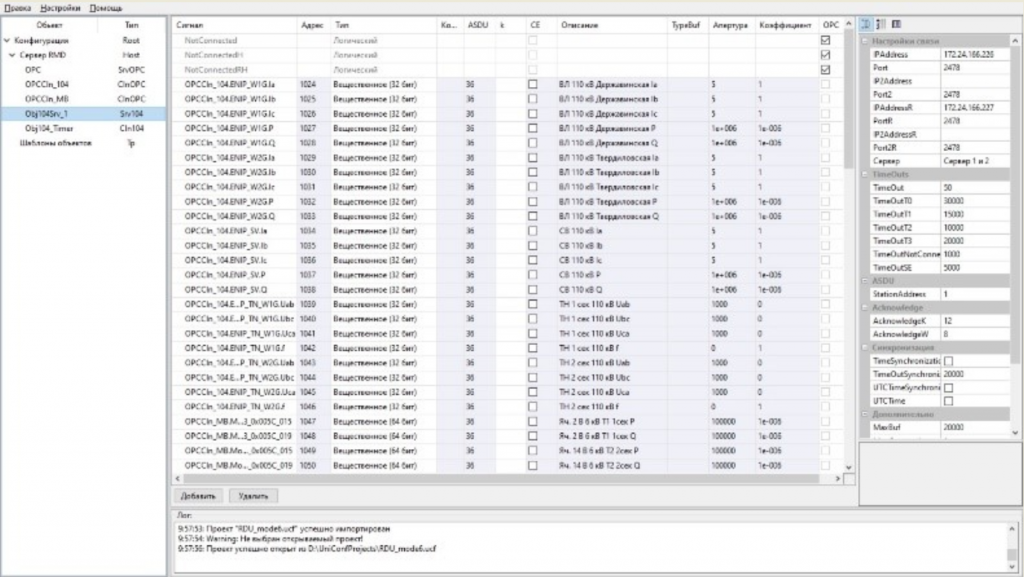
Window of setting for data transmission according to IEC 60870-5-104
|
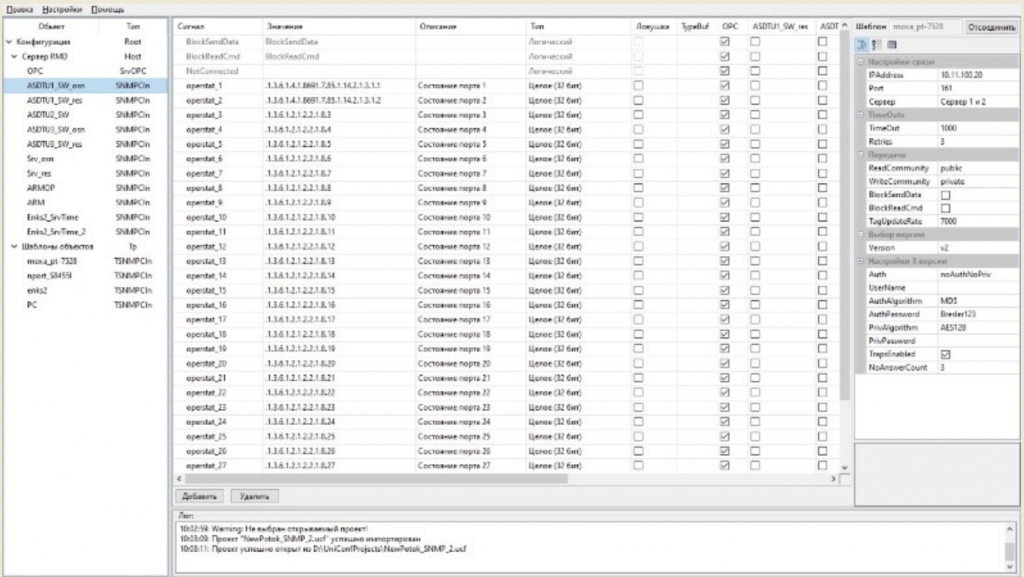
Window of setting for receiving data according toSNMP
|
STM-RLMK implements the information security function in terms of information protection. The basic set of technical information security measures includes:
1. Identification and authentication:
- the ability to set a password consisting of alphanumeric characters of upper and lower case, as well as special characters;
- the ability to limit the password expiration date;
- the ability to prohibit password reuse;
- the ability to notify the user about the need to change the password;
- storage of access passwords in a protected form;
- limiting unsuccessful login attempts.
2. Access control:
- the ability to configure access rights for users;
- the ability to control access at the role level.
3. Software environment limitation:
- installing updates only from a registered flash drive.
4. Protection of machine media of information:
- booting the operating system only from a registered flash drive.
5. Security event logging:
- users entry/exit registration;
- registration of system errors;
- registration the installation of updates.